Privacy Policies
How we Process your data
1.Privacy Policies
Security & Privacy is in our DNA and hence data privacy is our highest priority. This security overview provides a high-level overview of the security practices put in place to achieve that objective. Feel free to reach out to us at technology@arishti.in We track the location of the user -- based on the permission granted by her/her will. We will never provide any part of your information to anyone unless consented/bound legally in case of any data breaches.
2.Platform Security
MeMe’s Microservices is hosted and deployed on Azure Cloud Services. We follow MACH architecture using the most secure services of Azure. MeMe strictly follows the Zero Trust Framework, making the platform most secure, high-performing, scalable, and efficient.Distributed Denial-of-Service (DDoS) attacks are prevented using the multi-level defence firewalls and Database hardening at server level.
3.Information Security
We are currently using a Patent-pending Quantum Security architecture, which makes the platform highly secure in itself. All users' data is completely encrypted at all times. We provide both in-transit and at-rest encryption.The military-grade TLS based encryption algorithm, which helps in protecting users' data from Man-in-the-middle and eavesdropping attacks, are being used to provide the utmost security to the platform. We provide End-to-End enterprise grade AES 256 encryption. Our platform has an intelligent logging system which logs and audits the intrusion into the system from any unknown sources. We utilize data replication for data resiliency and disaster recovery as well as backup testing for data reliability. On the top of it, the platform has been configured with role-based access control to secure the sensitive organizational data
4.Application Security
We have implemented a strong password policy and a mandatory Two-Factor Authentication (2FA) protocol with One Time Passcode for user login and SignUp.
5.Consent Over the Data
At Arishti, we believe that the Consent is the future of Security and hence the complete platform is being built in consideration of the same. We do not permit the other users to use/share your data without your consent or at some places warning you with the system intimations.
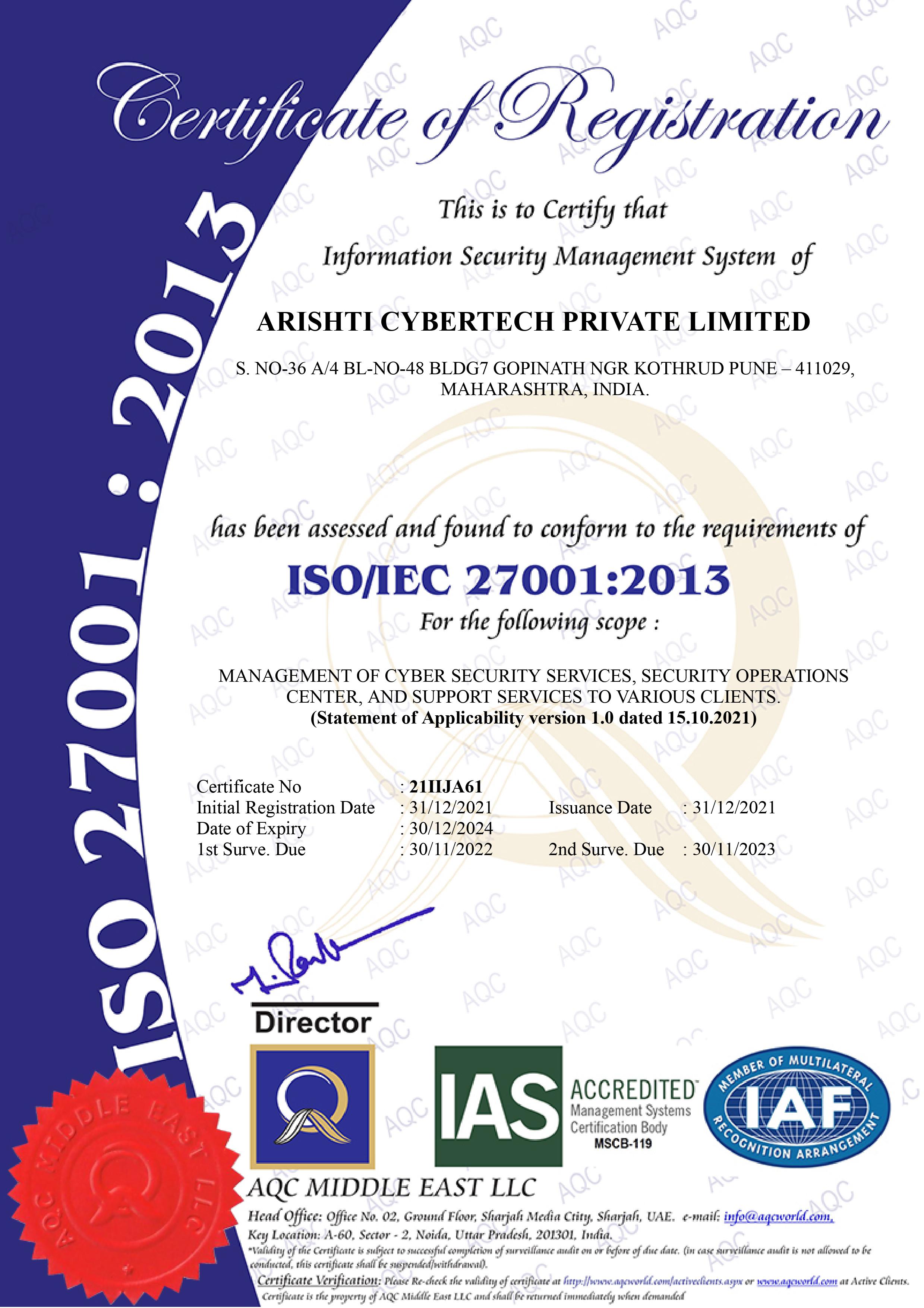
6.ISO 27001::2013 Certified
Our platform processes and the management has been verified and certified through ISO 27001::2013 standard. This itself proves our trust and the priority towards our data security and privacy management for the enterprises.
7.Legal Disclosure:
We are committed to keeping our customer’s data secure and private. Keeping up with our users' trust, we have implemented the highest grade of security standards. Despite our best efforts, if you are a technology expert or a security researcher and come across any potential security vulnerability problems, we encourage you to report the same responsibly by writing to us at technology@arishti.in along with the encountered issue screenshot and detailed process required to regenerate the vulnerability at our end. We assure you to fix the issue after carefully evaluating the said vulnerability within the minimum time frame. Kindly note that though we appreciate your experience and expertise, if the vulnerability has been used for unlawful gains, we might take legal actions against you. Your report shall be considered confidential. Your private data is not usually shared with our third party partners at any time, unless it is a legal obligation.
8. Grievance Officer
We are committed to keeping our customer’s data secure and private. In case you have any doubts/queries about the data processing or its usage, you can contact or write to our Grievance Officer Mr. Kanak Kawadiwale (kanak.k@arishti.in) along with the details of your query.